Fraud Reduction
What Is E-commerce Fraud?
eCommerce fraud is an illegal transaction performed on an eCommerce platform by a criminal or fraudster by using stolen payment information for online transactions without the account owner’s knowledge. It is also known as purchase fraud. It can be done by using a false identity, stolen credit card, fake cards, and details, false personal and card information, etc.
Fraud prevention is a top priority for business owners. Advanced fraud techniques and rapid growth in fraudulent credit card activity, especially in ecommerce, make adherence to the Payment Card Industry Data Security Standard (PCI DSS) strictly enforced for businesses that accept electronic payments. There are many simple safeguards you can implement at your business to reduce your risk of fraud.
Types of Ecommerce Frauds we Protect against:
Identity theft:
Identity theft or identity fraud takes place when an impostor obtains and uses personally identifiable and financial information of another person. This is the form of illegal impersonating. It is the unauthorized use of personal and financial data.
This fraud not only affects customers but equally affects the merchant, as customers can place a refund request.
Customers may feel that their personal and financial data is vulnerable and can not be shared on the eCommerce websites or web-shops are less likely to checkout. This can cost a store's reputation to dip.
Account takeover is a form of identity theft, in which the fraudster gains access to the user’s account and engages in fraudulent activity.
This can be done by a variety of methods, like purchasing and hacking details like passwords, security codes, implementing phishing schemes, etc.
Chargeback fraud:
This is also known as friendly fraud. In this type of fraud, the customer keeps the goods/products purchased online from the eCommerce shop but still asks for a refund stating the purchase was never made or payment being made twice or item was never received.
Having a clear refund, reshipping, tracked shipping, and return policies for the e-store may help to reduce this ‘friendly’ fraud.
Clean fraud:
This fraud is done with the stolen credit card from a genuine user and is used to make an online purchase. The stolen card and card holder’s information is used to commit the fraud which looks like a legitimate purchase made by verified customers.
PCI Compliance:
The Payment Card Industry (PCI) Security Standards Council (an organization formed by the card brands) created the PCI Data Security Standard (DSS) to ensure that businesses follow best practices for protecting their customers’ credit card information.
Businesses fitting one or more of the following criteria are subject to the PCI DSS requirements:
- A business that accepts credit or debit cards for payment, even if using a third-party vendor’s hardware, software or application to do so;
- A service provider that stores credit/debit card data on behalf of another business; and/or
- A hosting provider or other service provider that processes or transmits credit/debit card data on behalf of another business.
What's the point of PCI compliance?
The same technologies that make everyday business efficient also make it easy for hackers to access sensitive information. That’s why a business taking “just a handful” of credit cards is no less obligated to protect that card data than the major retailer running thousands of transactions.
When fully and accurately implemented, the 12 requirements of the PCI DSS work together to provide your business with defense-in-depth; that is, multiple layers of security that make it much more difficult for an attacker to gain access to your customers’ sensitive data. Studies have shown that cyber thieves and their automated tools most often seek out basic mistakes such as weak passwords, misconfigured technologies and uneducated employees. The PCI DSS addresses these and other areas of weakness to effectively shield your business.
For more information on PCI Compliance, visit our FAQs Page!
How Products we sell Assist with Fraud Prevention:
The Authorize.Net Fraud Detection Suite benefits merchants by providing them with powerful tools to identify potentially costly fraudulent transactions while strengthening the security and reliability of their payment gateway account. Merchants have the ability to customize filter settings to match their individual business needs and control how the payment gateway handles suspicious transactions, including the ability to hold a transaction for manual review.
-
AVS – Enter your customer’s billing address through the Virtual Terminal or from your Web site, and the system will compare it to the address the card issuer has on file. Therefore, if someone is trying to use a stolen card to buy and ship items to a false address, this illegal activity will be detected and stopped before it occurs.
-
CVV – This is the Visa/MasterCard system involving a 3-digit number printed on the back of the credit card near the signature. It is used during authorization when the credit card is not present during the transaction.
-
Velocity Filter – Limits the total number of transactions received per hour, preventing high-volume attacks common with fraudulent transactions.
-
IP Address Blocking – Allows merchants to block transactions from IP addresses known to be used for fraudulent activity.
3rd Party Fraud Protection Software:
3-D Secure:
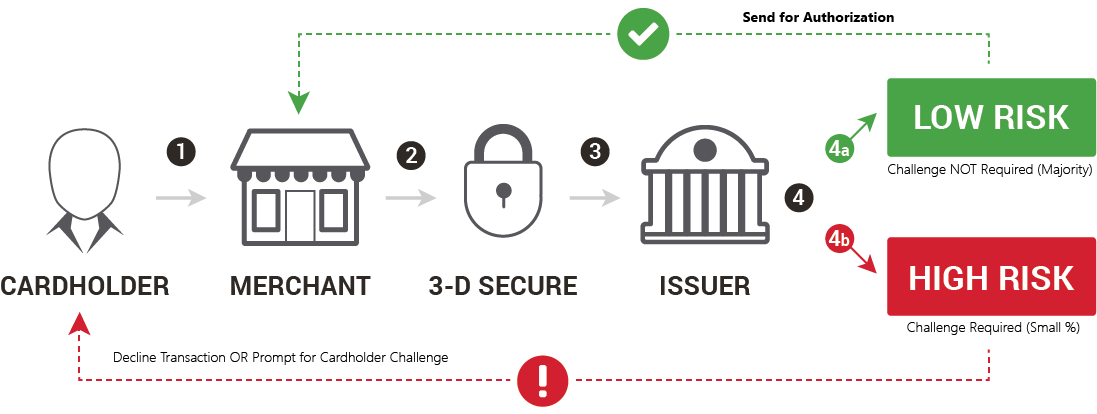
3-D Secure helps to minimize costly fraudulent transactions by adding an extra layer of protection to the payment process. The solution enables issuers to authenticate the cardholder using various available methods—from a one-time password to biometrics. Successful authentication helps confirm that the transaction comes from a real cardholder. This makes it more likely that the transaction will be authorized.
Our solution can silently authenticate most transactions by verifying customer data with the card issuer. For high-risk transactions, customers will be asked for additional authentication.
Kount: